A multitude of effective phishing schemes lead to monetary losses or malware infiltration. However, falling victim to certain phishing cons, particularly those currently aimed at Russians seeking information about organizations opposing the Kremlin’s military actions, could endanger both your liberty and your life.
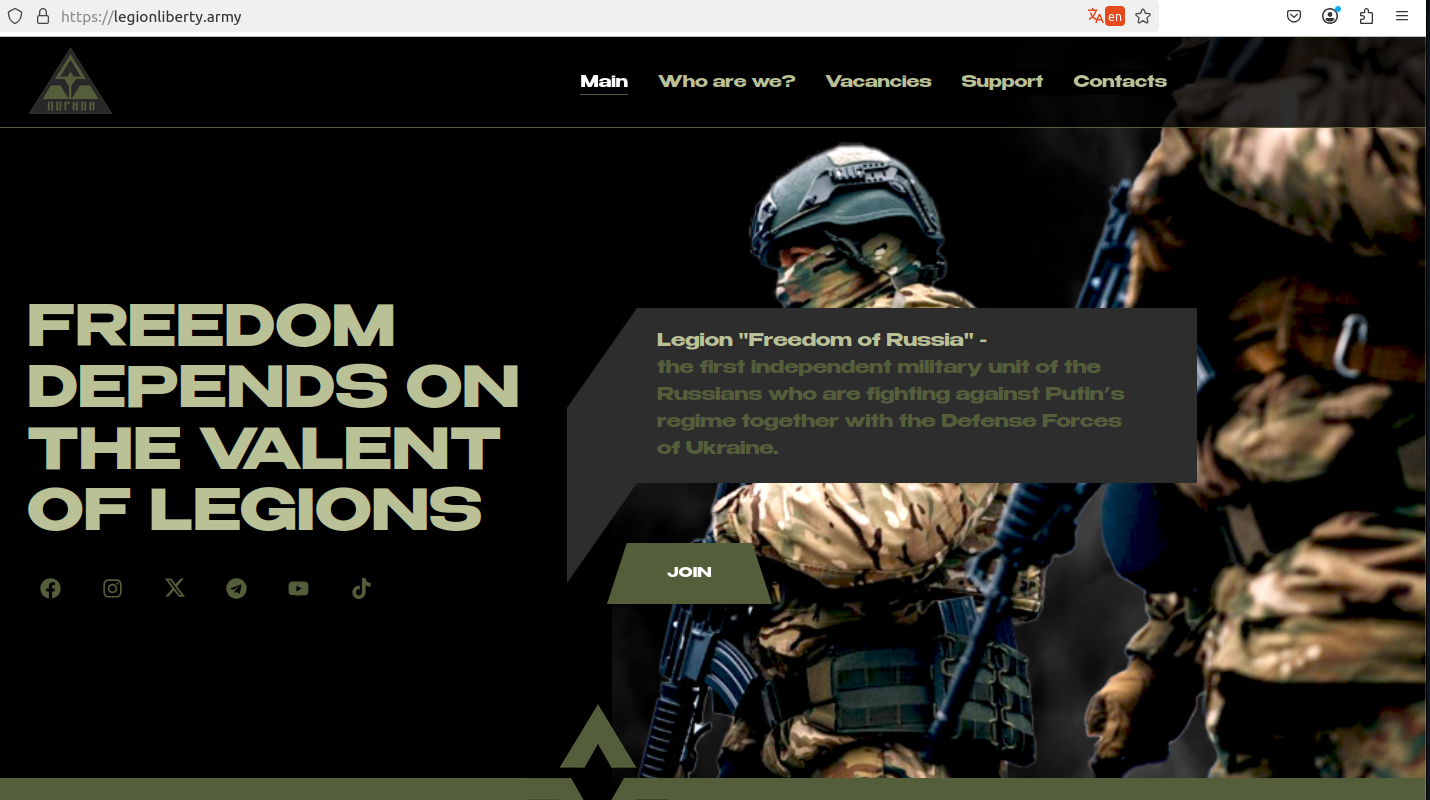
The authentic website of the Ukrainian paramilitary group “Freedom of Russia” legion. The text has undergone machine translation from Russian.
Experts at the security company Silent Push identified a network of numerous phishing domains that imitate the recruitment platforms of Ukrainian paramilitary organizations, in addition to Ukrainian governmental intelligence websites.
The webpage legiohliberty[.]army presents a near-exact duplicate of the homepage for the Freedom of Russia Legion (also known as the “Free Russia Legion”), a paramilitary unit based in Ukraine comprised of Russian nationals who resist Vladimir Putin and his invasion of Ukraine.
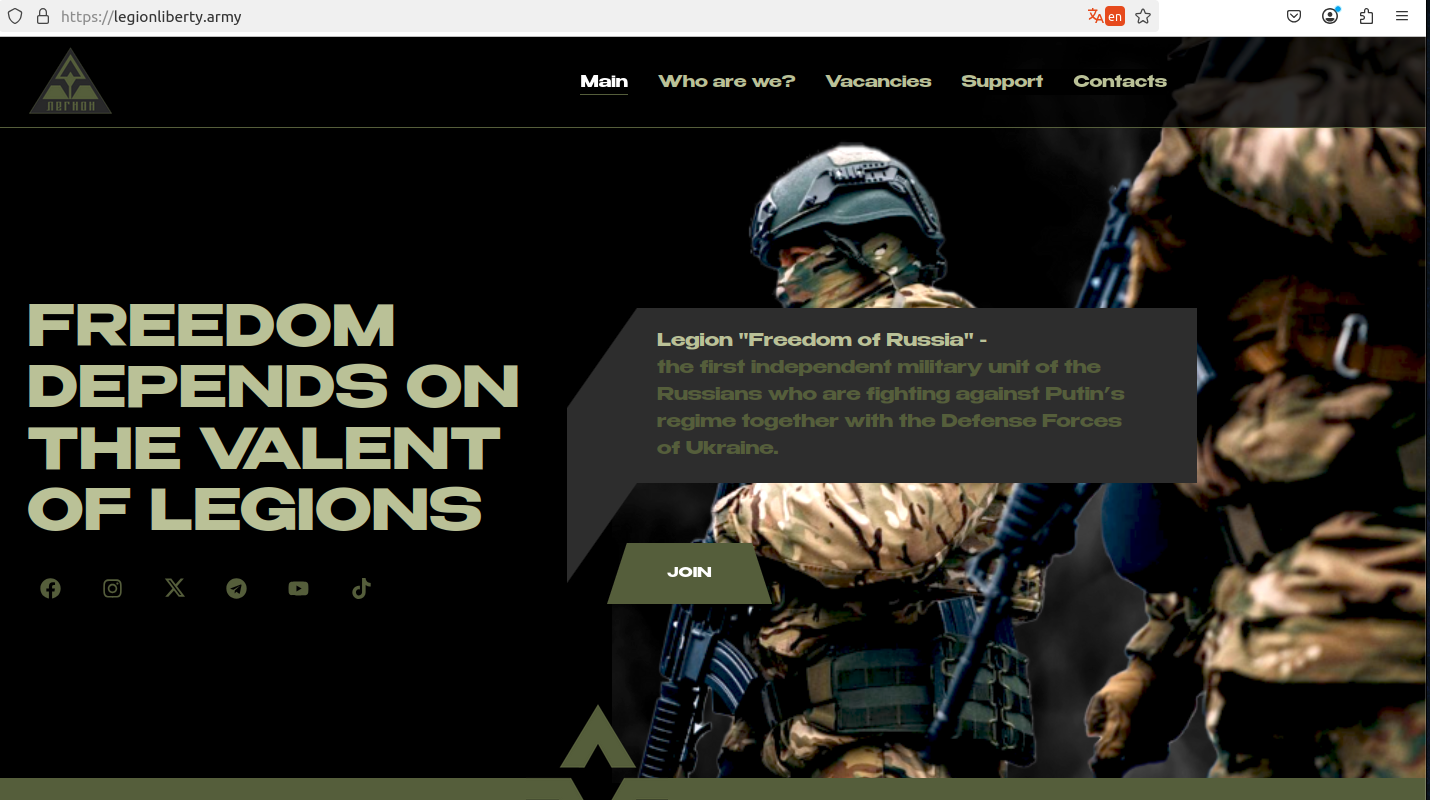
The counterfeit version of that webpage mirrors the authentic site — legionliberty[.]army — offering an interactive Google Form where prospective applicants can submit their contact and personal information. The form solicits visitors to provide their name, gender, age, email, and/or Telegram handle, country, nationality, military experience; political opinions; reasons for joining; and any undesirable habits.
“Engaging in such anti-war activities is deemed illegal in the Russian Federation, and participating individuals are frequently prosecuted and detained,” Silent Push stated in a report published today. “All observed campaigns shared similar characteristics and had a common aim: gathering private data from victims visiting the website. Our team suspects that this effort is likely orchestrated by Russian Intelligence Services or a threat actor with similar goals.”
Silent Push’s Zach Edwards indicated that the fraudulent Legion Liberty site had numerous connections with rusvolcorps[.]net. This domain imitates the recruitment page for a Ukrainian far-right paramilitary organization termed the Russian Volunteer Corps (rusvolcorps[.]com), and utilizes a comparable Google Forms page to gather data from potential members.
Additional domains that Silent Push linked to the phishing plot include: ciagov[.]icu, which duplicates the content from the official site of the U.S. Central Intelligence Agency; and hochuzhitlife[.]com, which imitates the Ministry of Defense of Ukraine & General Directorate of Intelligence (whose genuine domain is hochuzhit[.]com).
According to Edwards, there are no indications that these phishing websites are being advertised through email. Instead, it appears that the individuals behind them are promoting these sites by manipulating the search engine results when someone searches for one of these anti-Putin entities.
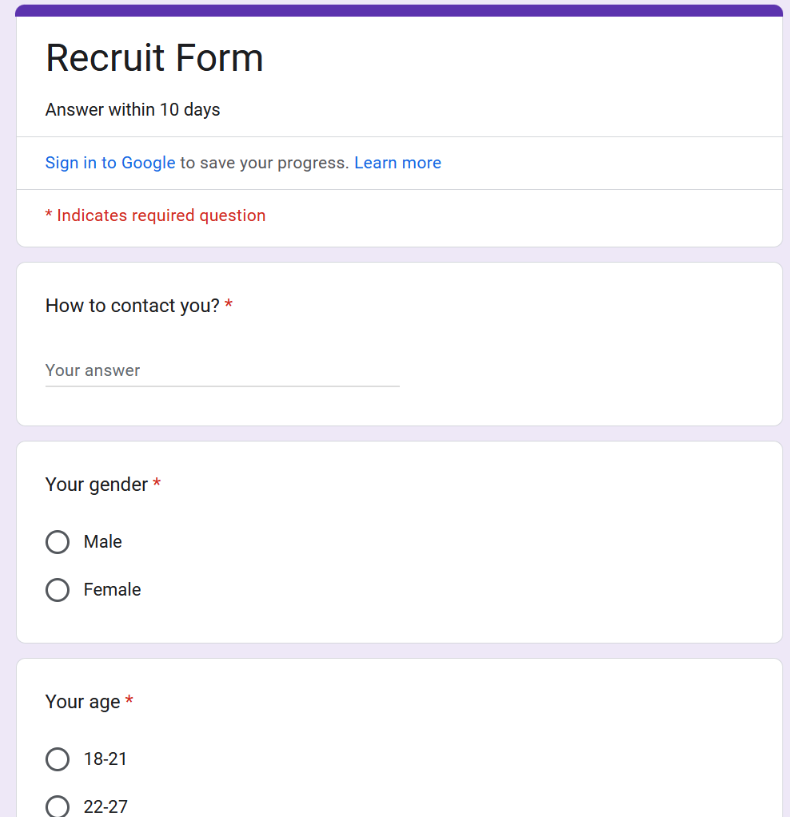
In August 2024, cybersecurity researcher Artem Tamoian shared on Twitter/X about receiving surprisingly different results when he investigated “Freedom of Russia legion” in Russia’s leading domestic search engine Yandex compared to Google.com. Google returned the legitimate website as the top result, while the primary result on Yandex was a phishing page aimed at the group.
“I believe at least some of them are being promoted via search,” Tamoian remarked regarding the phishing domains. “My initial thread accused Yandex, but besides Yandex those sites consistently rank above legitimate ones in DuckDuckGo and Bing. Initially, I didn’t grasp the extent of it. They keep appearing even now.”
Search results from DuckDuckGo on Mar. 27, 2025, for “Freedom of Russia legion” indicate that the first result returned is a phishing domain.
Tamoian, a native of Russia who departed the nation in 2019, is the founder of the cybersecurity investigation platform malfors.com. He recently uncovered two additional sites impersonating the Ukrainian paramilitary groups — legionliberty[.]world and rusvolcorps[.]ru — reporting both to Cloudflare. Following Cloudflare’s action to block these sites with a phishing warning, the actual Internet address of these sites was revealed to belong to a notorious “bulletproof hosting” network known as Stark Industries Solutions Ltd.
Stark Industries Solutions emerged two weeks prior to Russia’s invasion of Ukraine in February 2022, appearing suddenly with hundreds of thousands of Internet addresses in its possession — many of which were initially allocated to Russian governmental entities. In May 2024, KrebsOnSecurity published an in-depth report on Stark, which has repeatedly been utilized to host infrastructure for distributed denial-of-service (DDoS) assaults, phishing, malware, and misinformation efforts from Russian intelligence organizations and pro-Kremlin hacker collectives.
In March 2023, Russia’s Supreme Court classified the Freedom of Russia legion as a terrorist organization, implying that Russians found communicating with the group could face prison sentences ranging from 10 to 20 years.
Tamoian remarked that those seeking online information about these paramilitary groups have become easy targets for Russian security agencies.
“I began investigating those phishing websites because I kept encountering reports of individuals being detained for attempting to join [the] Ukrainian Army or for seeking to assist them,” Tamoian expressed to KrebsOnSecurity. “I’ve also observed accounts of FSB reaching out to individuals impersonating Ukrainian officials, alongside the usage of counterfeit Telegram bots, which led me to consider that fake websites could also be a possibility.”
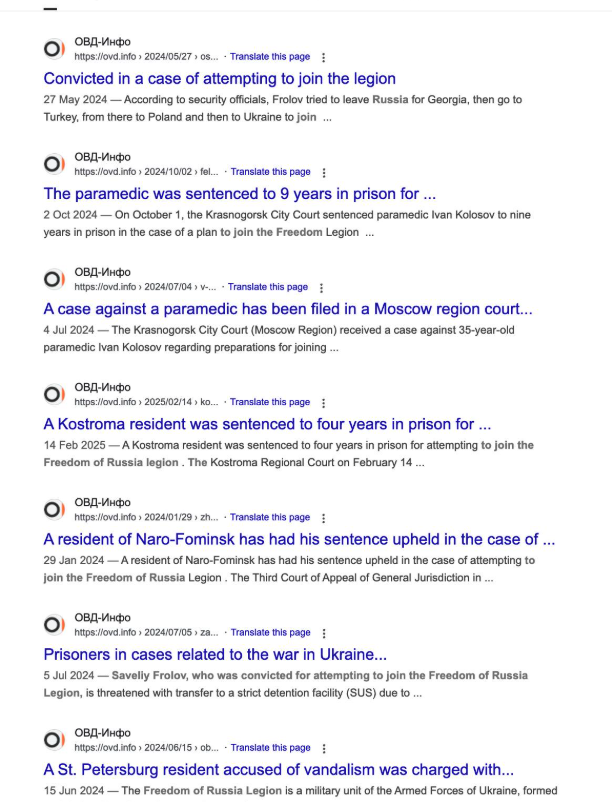
Search results demonstrating news articles about individuals in Russia receiving long prison sentences for attempting to assist Ukrainian paramilitary organizations.
Tamoian noted that reports frequently arise in Russia regarding individuals being apprehended for trying to execute an action requested by a “Ukrainian recruiter,” with courts invariably imposing severe sentences regardless of the individual’s age.
“These incidents keep occurring, but generally, there are no specifics regarding how individuals are actually apprehended,” he mentioned. “All cases connected to state treason [and] terrorism are classified, leaving scant information.”
Tamoian stated that while he lacks direct evidence linking the reported arrests and convictions to these phishing websites, he is convinced that the sites are part of a wider campaign orchestrated by the Russian government.
“Given that they maintain these websites and continue to generate more, I suspect it might be an effective strategy,” he remarked. “They dominate DuckDuckGo and Yandex search results, which regrettably yields results.”
For further reading: Silent Push report, Russian Intelligence Targeting its Citizens and Informants.